Do you have an old PC lying somewhere with a lot of dust all over it ? Do you want a local data cloud to sync all your files across your laptop, tablet, PCs ?
Then, I guess this tutorial will come in handy.
– First step is to dust your machine off , when I first plugged in my machine it didn’t even boot except when I really cleaned it well but sadly one RAM stick died because of dust . Now I am stuck with only 256 MB of RAM on my P4 2.8 GHZ machine but that didn’t set me back !
– Download, burn and install your favorite Linux distro as ownclowd supports many distros, but note that this tutorial is debian-based, I am using debian wheezy 7.4 standard(no desktop)
– Remember that we are dealing with a server now:
- It’s important that when the machine restarts because of a power cut for example; it should always boot to your server OS without any external intervention because we will only use ssh and won’t connect any IO devices to the server machine (keyboard,mouse,monitor…etc.) , also make sure to configure your BIOS settings (boot device, order..etc.) .
- To save power disconnect any unneeded peripherals(for ex: I disconnected my Nvidia VGA card and DVD ROM ) , not sure if it will do much saving for this old machine but better than nothing.
– Set a static IP to your local server , for a Debian server you can follow the following instructions from elinux which were originally written for the raspberry pi but the will work perfectly here:
You only need to modify the file /etc/network/interfaces
Before you do, backup the current version of the interfaces file, if there is already one present:
pi@raspberry:sudo cp /etc/network/interfaces /etc/network/interfaces.sav
You can edit the file with any text editor such as vi or vim.
We need root privileges, so we use sudo:
pi@raspberry:sudo vi /etc/network/interfaces
In the interfaces file look for a line such as:
iface eth0 inet dhcp
This is to enable the DHCP client. You do not want this to work any more.
Put a hash at the beginning of the line to disable it or delete it:
#iface eth0 inet dhcp
In the file you must insert the following lines:
# The loopback interface auto lo iface lo inet loopback auto eth0 iface eth0 inet static #your static IP address 192.168.1.118 #your gateway IP gateway 192.168.1.1 netmask 255.255.255.0 #your network address "family" network 192.168.1.0 broadcast 192.168.1.255
Only the address and netmask data are strictly required.
If for example your LAN is configured to have IP adresses in the range x.x.x.1 to x.x.x.255, you will put x.x.x.0 in the network line.
“address” is the IP you want the RPi will assume (in the proper range, as described above). pay attention not to use an IP already used by another device in your LAN or that can be assigned to a device by your router by DHCP (set the DHCP range of the router wisely in order to avoid potential overlaps).
“netmask” will “always” be 255.255.255.0
gateway is usually x.x.x.1 (your router IP or the one given by your ISP)
You now need to restart the network:
pi@raspberry:sudo /etc/init.d/networking restart
– Install ownclowd using the following techcint great tutorial , I recommend you to fully read it to understand what you are doing but here is a cheat sheet of the commands
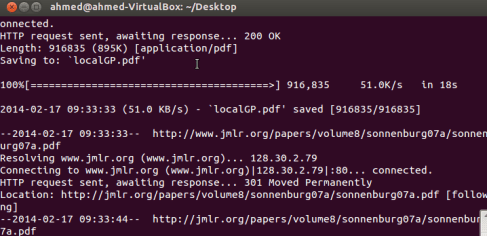
# apt-get install apache2 apache2-doc apache2-utils mysql-server mysql-client php5 php5-mysql php5-gd # mysql -u root -p mysql> create database cloud ; Query OK, 1 row affected (0.00 sec) mysql> grant all on cloud.* to yourname@localhost identified by 'my_password'; Query OK, 0 rows affected (0.00 sec) # wget http://download.owncloud.org/community/owncloud-6.0.0a.tar.bz2 # cp owncloud-6.0.0a.tar.bz2 /var/www/ # tar -jxvf owncloud-6.0.0a.tar.bz2 # rm -rf owncloud-6.0.0a.tar.bz2 # chmod -R 777 owncloud/ # a2enmod rewrite # a2enmod headers # nano /etc/apache2/sites-available/default
Find
AllowOverride None
Change this to:
AllowOverride All # service apache2 restart
VOILA ! You should be up and running now using : http://your-ip-address/owncloud
Now , you should create the admin user and remember to enter the mysql user and database to get it ready .
– Don’t go yet as there is a last step, php is set to have a max upload of 2 MBs which is useless so you have to configure it a bit :
Note: The order of the following steps is important! If you swap steps described below, the settings may fail.
Go to the admin section in the ownCloud-WebUI and do the following:
- Under “File handling” set the Maximum upload size to the desired value (e.g. 16GB)
- Click the “save”-Button
Open the php.ini – file
- Under Debian or SUSE and their derivatives this file lies at /etc/php5/apache2/php.ini
- On Windows, you can find this file within C:/Program Files (x86)/PHP/PHP.ini
Do the following:
- Set the following three parameters inside th php.ini to the same value as chosen inside the admin-section one step before:
- upload_max_filesize = 16G (e.g., to stay consistent with the example value above)
- post_max_size = 16G (e.g., to stay consistent with the example value above)
- output_buffering = 16384 (e.g., to stay consistent with the example value above)
whereas the “output_buffering” has to be given in MegaBytes but as a plain figure (without size-units as ‘M’ or ‘G’)
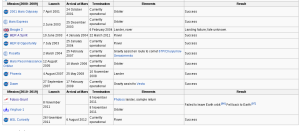
These client configurations have been proven by testing maximum file sizes of 16 GB:
- Linux 32 Bit: Ubuntu, Firefox => 16GB
- Windows 8 64 Bit: Google Chrome => 8GB
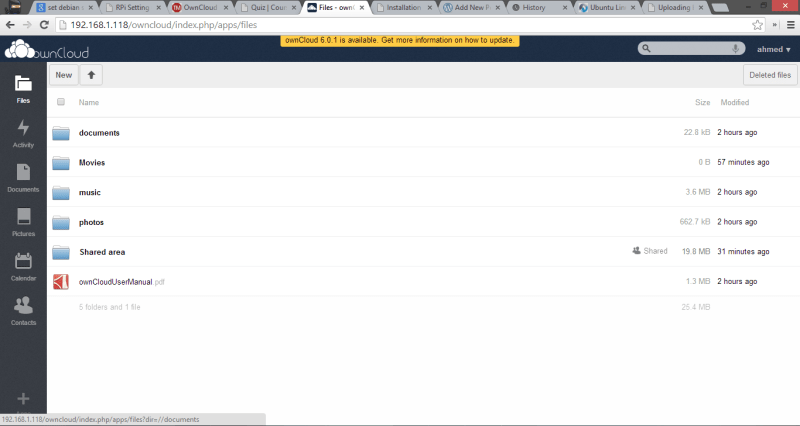
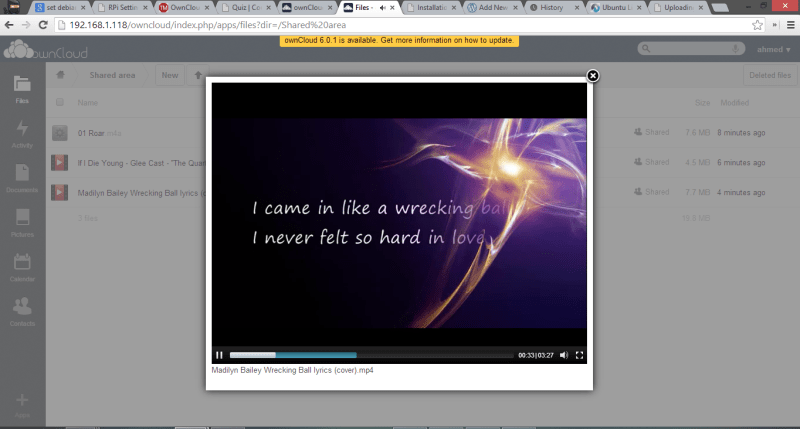
Here are some screenshots of my local cloud !