Problem Statement
There is a growing demand of automotive OEMs for a POSIX software OS that is capable of powering up a complex centralized multimedia ECU that drives multiple usecases including safety ones such as Instrument Cluster, ADAS, and others, in addition to non-safety applications for entertainment as Navigation , phone ..etc.
This demand is met with a shortage of solutions in the market, leading to the necessity of combining multiple OSes from different vendors which yields a complex software architecture , and a cumbersome integration process by design. Moreover, in most cases the market is monopolized by a single or a few players, putting most OEMs in a vendor lock-in situation , on top of finding it very expensive to get the right talent from the market for closed source technologies.
These factors put legacy OEMs in a vulnerable position against rising threats from the US and China. The latter can deliver new software solutions at a much higher speed by relying on open source, adopting simpler architectures, disregarding some of the existing standards, and taking bolder decisions.
The legacy OEMs need a software solution that enables them to develop software with higher speed while still abiding to the legal frameworks and the existing automotive standards. They need to break free from the vendor lock-in situation and explore new technologies that offer more flexibility, cost-effectiveness, and efficiency.
Overview of some solutions in the market
| QNX | NEW! Redhat Vehicle OS | Adding a separate AUTOSAR controlloer |
| Battle tested in Automotive | One known automotive customer | Battle tested in Automotive |
| * Closed-source * Less talent in the market * Expensive * Monopoly | * Open source * Big pool of talent * Will it be expensive too ? | * Open standard, open-source-when-you-pay * Big pool of talent * Expensive * Complex architecture * Nearly a Monopoly * Outdated tools and workflows |
Using ChatGPT to develop a safe Linux distribution
Can we employ the power of ChatGPT to establish a fast and simplified certification/recertification process to deliver a safe Linux distribution according to the ISO26262? ChatGPT usecases to investigate:
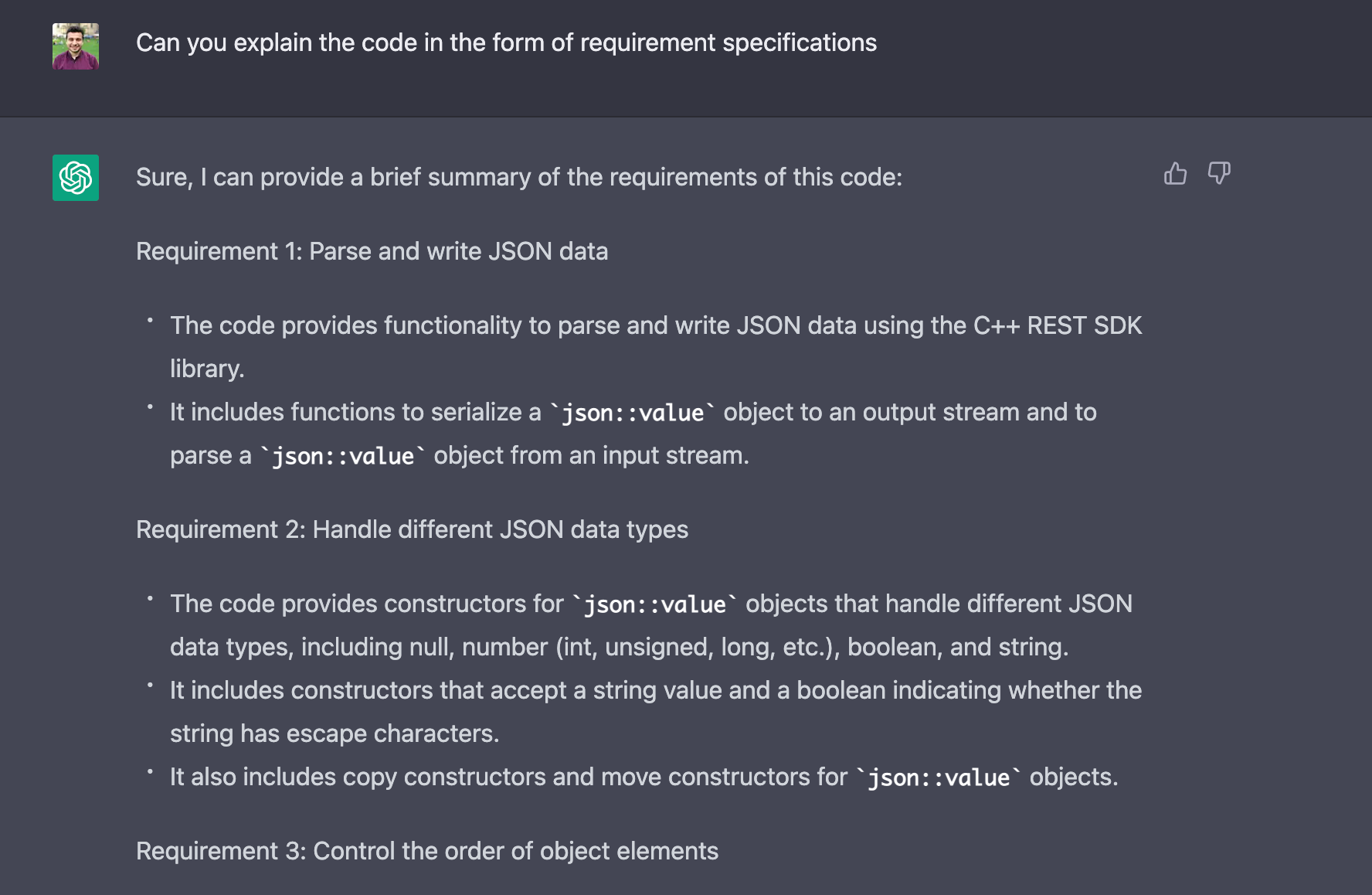
- Can ChatGPT write software requirements from a given code implementation?
- Can ChatGPT write software requirements from a high level description of a software package?
- Can ChatGPT create architectural diagrams?
- Can ChatGPT write unit tests from a given code implementation?
- Can ChatGPT increase test coverage?
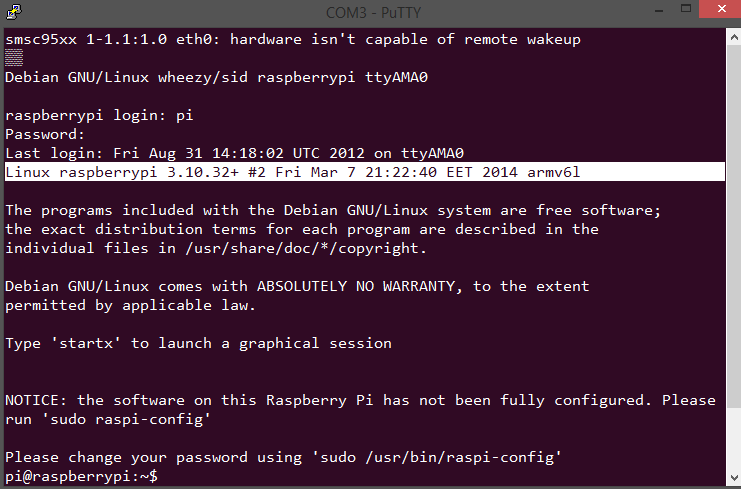
Usecase for investigation CPPRESTSDK (medium size software package)
- There is no way (so far) to give a whole git repo to be analyzed by ChatGPT
- However, OpenAI has promised to release several plugins that will allow ChatGPT to read files and/or access the internet
- It doesn’t seem that ChatGPT can build the context of the whole project and it gets lost when the code snippet provided to it is too long
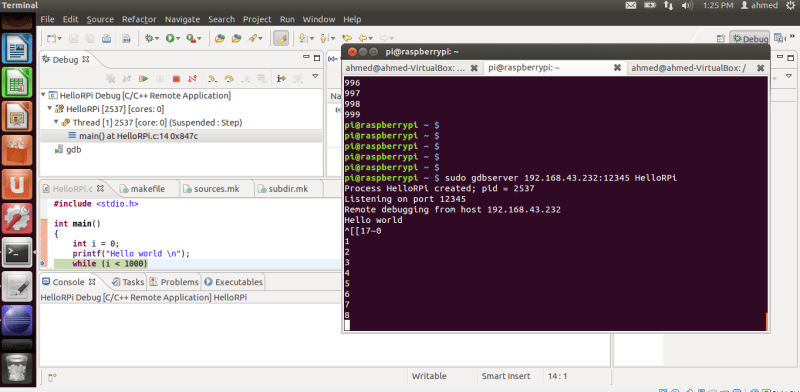
- For example, it selectively explained a subset of functions when I provided a file of 500 lines
- It couldn’t process a larger file ~ 1k lines
- When I asked it to give a really detailed analysis , it started spitting out description of imaginary functions that I didn’t ask about at all!
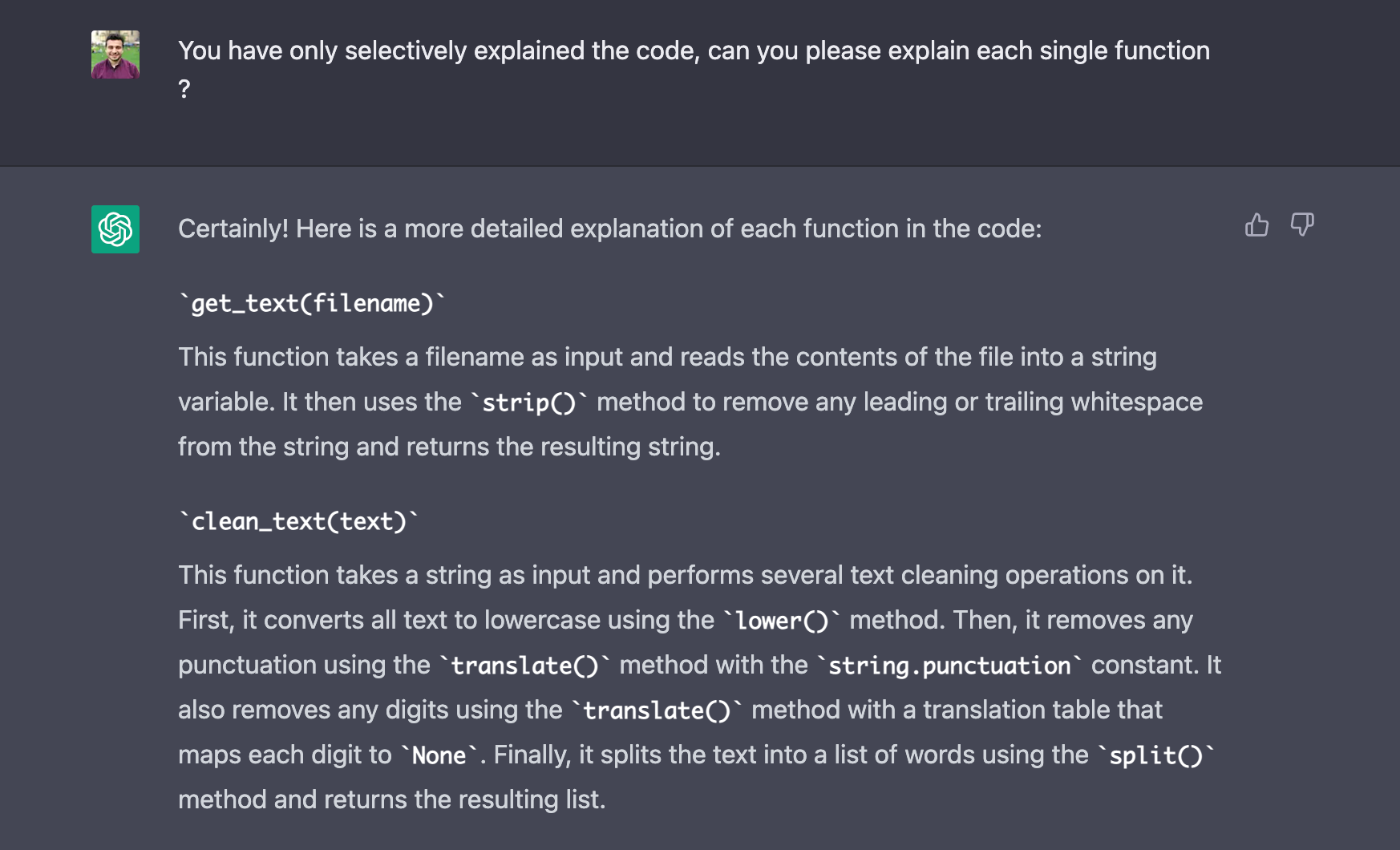
- ChatGPT was able to provide an explanation to a piece of code in the form of requirements specifications
- ChatGPT was able to perform on a much higher level when presented with a single simple c function , it could come up with 2 high quality test cases
Conclusions
- For any kind of realistic results, a code needs to be broken down into smaller pieces before feeding it into ChatGPT, then the output still also needs human supervision and review.
- Humans will need to create context and analyse the workpackages. Detailed plan of work to be created as if a team will do it with no AI assistance.
- AI can then kick in and speed up the execution of single tasks and improve the overall timeline of the project.
- The final output shall be orchestrated and delivered by humans
- ChatGPT is a resourceful and a smart assistant, but in a complex narrative I would regard it as a supporting character or a “CoPilot”
- ChatGPT can spit out completely wrong information with a very confident tone
- Software Engineers can rest assured that their jobs are not being replaced anytime soon, however the expectations of the efficiency of someone will drastically change, and the gap between a SWE+Copilot vs an old school SWE will be tremendous